Remote Access is Essential for Enterprises
Simply put, secure remote access helps enterprises leverage the power of widespread network connectivity to access devices, networks, or platforms located in different locations to improve productivity and efficiency.
Despite security risks, for most enterprises, locking down remote access is not viable as it continues to be an essential tool. For example, global companies need to remotely manage device inventory, regardless of the devices’ physical locations.
Internal IT teams use remote access to patch or fix devices, especially if something breaks during a global software update. OEM vendors need to remotely access customer devices for repairs and troubleshooting activities like transferring files or collecting logs.
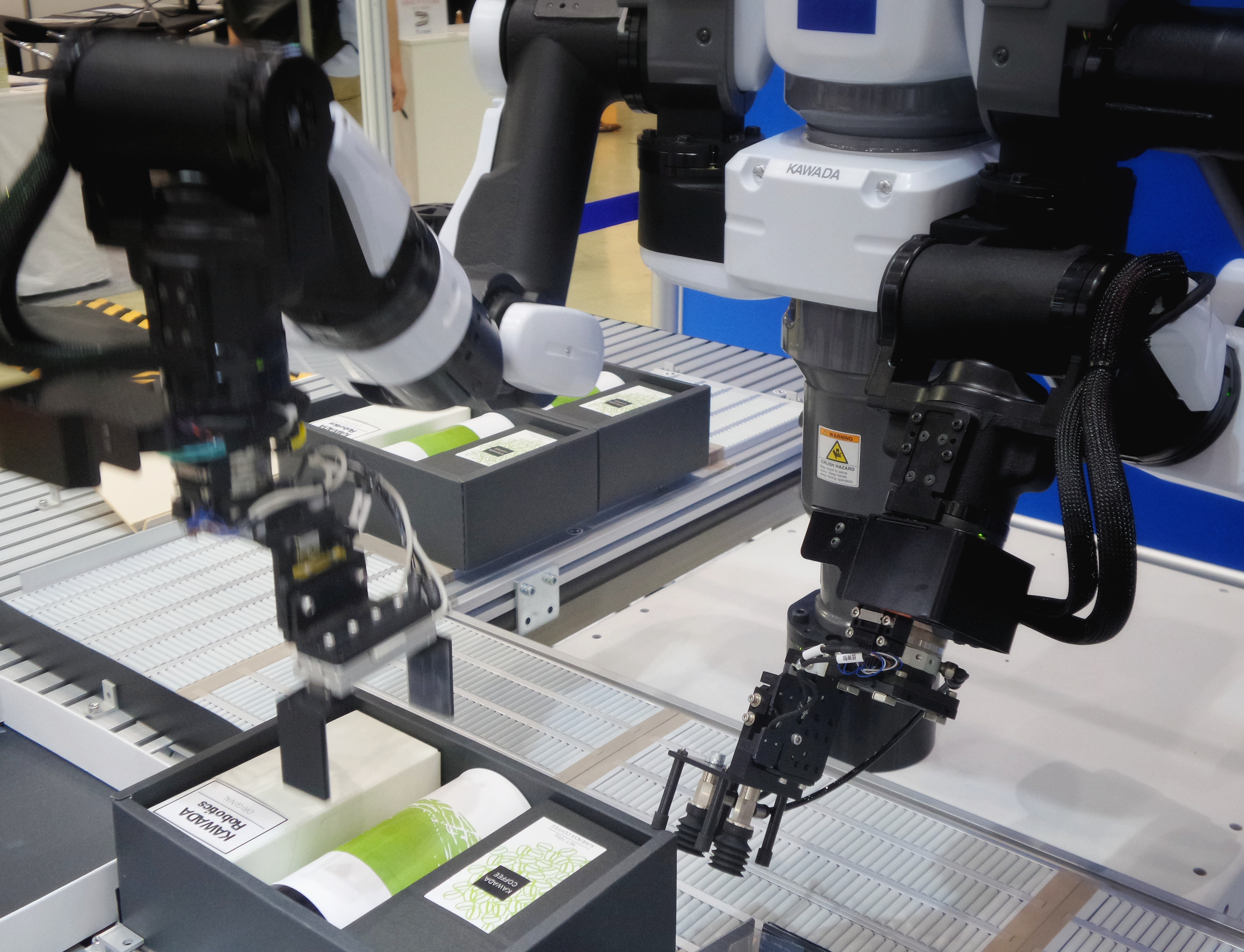
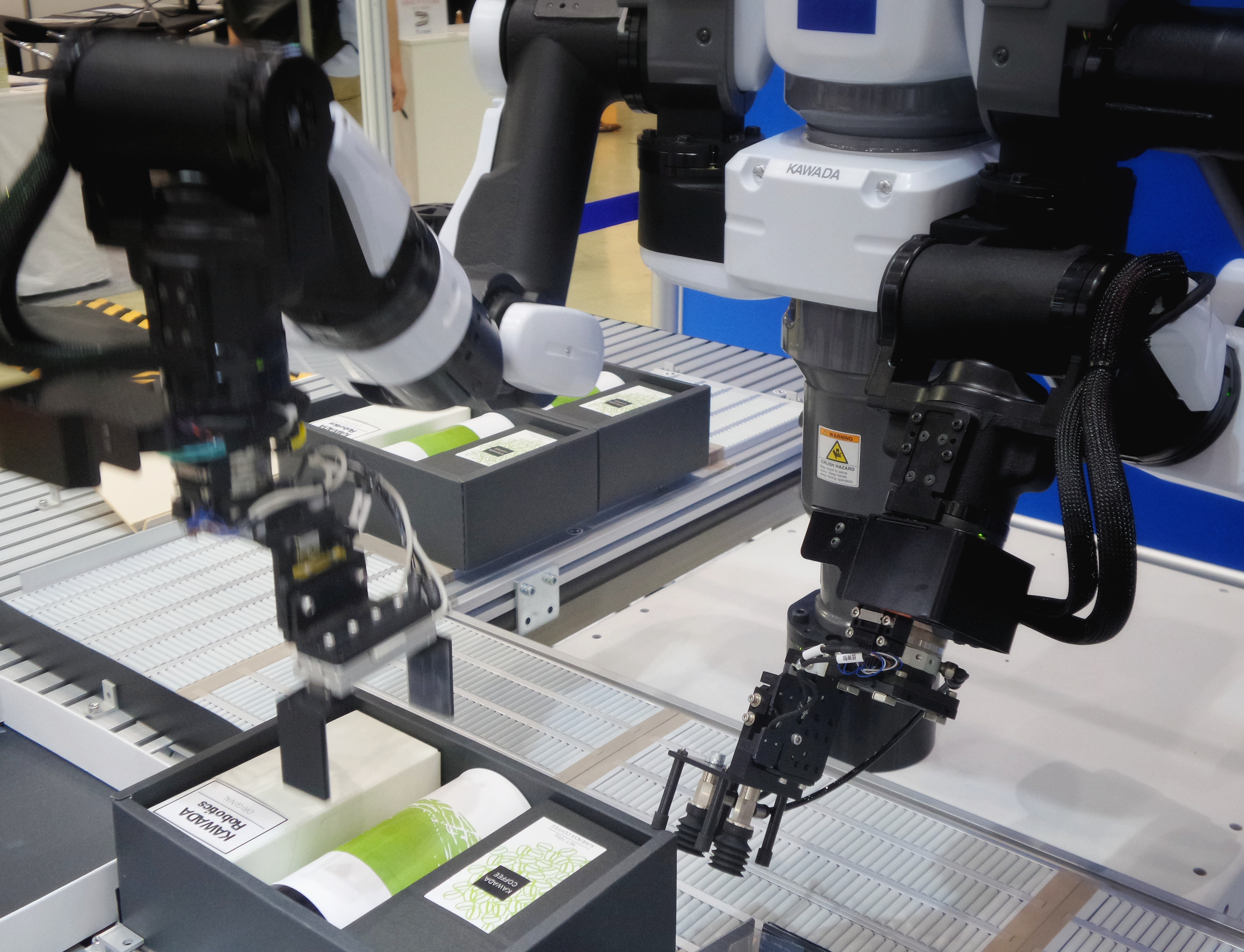
The Internet of Things (IoT) enables traditional equipment on factory floors, mining rigs, energy and power plants, and other facilities to be network connected for remote monitoring and management.
Download the full whitepaper here.
Overcoming Security Limitations of Remote Access Solutions
For years, cyberattacks have exploited remote access vulnerabilities to inflict deeper damages in organizations. But recently, the increasing shift to distributed offices escalated those risks. A more remote workforce, along with complex third-party supplier ecosystems, made remote access a rampant threat vector.
Microsoft’s Remote Desktop Protocol (RDP), already a common target for man-in-the-middle attacks, Introduction contributed to a 768% rise in attacks in 2020. The cyberattack targeting SolarWinds (December 2020) is another example of this trend. In SolarWinds, similar to NotPetya, the attackers gained access to a trusted update channel by compromising a software provider.
These evolving threats justify the jittery outlook among CISOs, security experts, and IT professionals with remote access usage. Whitepaper With remote employees and cloud sprawl to consider, it has never been harder to manage the security perimeter. IT security teams must detect unauthorized access quickly and limit horizontal movement in the network to protect sensitive data.
In February 2021, a data breach on Walmart’s data hosting supplier allowed PII of Walmart’s pharmacy patients to be stolen. The breach resulted from unauthorized remote access into the service provider’s servers. Companies have traditionally relied on Virtual Private Networks (VPN) to secure remote access. But a VPN connection only goes so far.
One big challenge is that once attackers get access to a VPN, they can easily penetrate the network like to maintain uptime regardless of where your IT team physically resides. On the hind side, remote access increases security and compliance risks. It is essential to protect devices from these heightened risks. These devices often process sensitive data from customers, patients, employees and more.
If there’s a data breach, there’s a compliance risk to those individuals and the organization. These operational devices in factory floors or hospitals sometimes run on outdated Windows or Linux systems. Hackers usually target those systems as a way to get a foothold in an organization’s network.
Companies in highly regulated industries have to be cautious about devices on their networks. That includes ATMs, POS devices in retail, kiosks, HVAC systems, IIoT factory floor robots, and healthcare devices (imaging machines, MRI, X-ray). In highly regulated industries like healthcare, medical professionals have to send patient data through secure, encrypted channels or remotely monitor specialized medical devices. This must be done while fully complying with HIPAA, PHI, and ISO.
Banks and financial institutions remotely monitor ATM activities, supervise remote settlements, update and perform maintenance to reduce the cost of travel, truck rolls and costly in-person fixes. This has to be done using a remote access solution that’s PCI compliant. While being compliant is crucial, it is not the same as being secure. To secure the enterprise, you need a secure remote access solution with serious controls. a hot knife through butter. Many legacy firewall rules allow access to practically everything in the network. Management complexities with VPNs at scale expose additional security holes…



