

These threats to healthcare cybersecurity require a proportionate response from IT professionals in the industry. While conventional wisdom may be sufficient for some industries, cybersecurity in healthcare requires heightened protocols. By implementing additional security measures when remote access is required or beneficial, many healthcare organizations are fighting back against the increased threat of cybercrime.
In this guide, we’ll explore why the healthcare industry needs more protection and how to strengthen healthcare IT services.
Why is Cybersecurity Important in Healthcare?
Maintaining cybersecurity in healthcare is critical to safeguard your patients’ privacy and safety while reducing risk of costly interruptions in clinical care.
Healthcare facilities like hospitals, doctor’s offices, and pharmacies are welcome sites for cybercriminals because of the massive amounts of sensitive data transmitted, stored, and managed on servers, medical equipment, and mobile devices.
Now, providers and patients alike are moving more toward a model of distanced care, also known as telehealth. The COVID-19 pandemic has sent providers scrambling for even more solutions to maintain safe operations while caring for patients remotely. All of these challenges and trends open up healthcare systems to vulnerabilities that can be exploited by hackers and unauthorized parties such as:
- Doctors need to access patient files from home
- Medical office personnel need to access patient information remotely for billing and admin reasons
- IT service providers monitor, maintain and update office equipment that may store sensitive patient information
- Doctors & nurses need access to remote medical devices to review data
- Vendors and service providers need to access medical devices for maintenance, monitoring, and updates
What Are Common Healthcare Security Threats?


Let’s take a look at a few common cybersecurity threats that the healthcare industry faces and the potential impacts they may have on providers and their stakeholders.
1. Malicious Network Traffic
Privilege misuse, web applications, and miscellaneous errors account for 81% of cybersecurity incidents in healthcare according to a 2019 report by Verizon. Although this type of malicious network traffic might not be as coordinated as an all-out ransomware attack, their prevalence in the industry should put healthcare providers on high alert.
With healthcare services becoming increasingly spread out, the attack surface for cybercrime is much larger. Unauthorized downloads, apps, and websites allow malicious actors to move laterally within a provider’s network, opening them up to costly breaches and service interruptions.
Many healthcare organizations are adopting cloud-based services to improve patient care and collaboration. Even with the upside, these cloud-based apps can also be a point of vulnerability for malicious network traffic. And they can quickly become a compliance nightmare if third parties are granted access.
2. Ransomware Attacks
Ransomware is malicious software that encrypts valuable information until a sum of money has been paid. The victims of these attacks are often left with no way to access necessary files or data without paying the ransom.
In late October 2020, CISA, HHS, and the FBI released a joint report detailing how ransomware is becoming increasingly intricate when deployed in healthcare settings. Malware loaders TrickBot and BazaarLoader are used to deploy popular ransomware such as Ryuk and Conti.
These troubling developments in cybersecurity and healthcare IT signal that cybercriminals see lucrative ransoms to be won from organizations that are desperate to restore service and protect data.
3. Phishing Scams
Phishing refers to correspondence that appears to be from a trusted source but is actually intended to install malware and/or gain access to sensitive information such as login credentials or payment details.
Medical schools can’t prepare you for everything. From doctors and nurses to patients, recent data shows that all parties in healthcare are susceptible to phishing scams that put networks in danger. Whether it’s email, social media, or even by phone, these attempts to deploy harmful files are often the precursor to widespread ransomware attacks.
4. Outdated Legacy Systems
Legacy systems within hospitals and doctors’ offices are common for healthcare organizations operating on a budget or using older equipment. Unfortunately, these older operating systems represent a major weakness in healthcare cybersecurity. Without updates or regular patching, outdated operating systems become prime targets for cybercriminals.
Research suggests 83% of medical imaging devices operate on systems that are no longer eligible for software updates. These retired operating systems not only have outdated authentication, but their inability to be updated leaves the device they support as a potential foothold for hackers looking to gain deeper access into a provider’s network.
Data Breaches in Healthcare
Data breaches occur when unauthorized parties gain access to sensitive information within a private network. These breaches can be the result of several different tactics such as:
- Physical breaches – stolen laptops, hard drives, mobile devices, or even paper files
- Drive-by downloads – when a user unintentionally downloads malware by visiting a compromised website
- Weak authentication – hackers guess passwords to gain access to data
- Social engineering – like phishing, these attacks mislead users in order to download malicious attachments
The healthcare industry faces significant consequences from data breaches. If a data breach occurs in healthcare, organizations may be left without access to critical data, may be face costly legal battles for violating regulatory guidelines, and lose the trust of the public.
Given what’s at stake, medical institutions have an increased responsibility to maintain healthcare data security. A recent study by Privacy Affairs showed that 70% of Americans were affected by healthcare data breaches between 2009 and 2019.
The move toward distanced care coupled with a booming wearables market has brought about an explosion in electronic patient-reported outcomes, or ePRO. As the healthcare and biotech industries give patients the ability to report and track their own data, more sensitive information is being stored outside the confines of trusted networks.
These rapid advances in healthcare data collection improve public health but also lead to sensitive information being stored within vulnerable networks. Hacking groups know the value of this data and will try and exploit a network’s weaknesses to gain access.
Hospital Cybersecurity Trends & Telehealth


Even before the coronavirus pandemic, telehealth was on the rise. A recent study by the American Medical Association revealed that telehealth grew 53% between 2016 and 2017.
Now, in a healthcare industry overwhelmed by COVID-19, the numbers are even more staggering. A Centers for Disease Control and Prevention (CDC) study found that telehealth visits increased 154% in the last week of March 2020 at the emergence of the pandemic in the US.
Telehealth has enormous upsides for efficiency, safety, and convenience. But in terms of healthcare IT cybersecurity, these trends mean more information logged outside of providers’ local area networks (LAN). In order to prioritize cybersecurity, healthcare providers must ensure that their telehealth applications are backed with appropriate encryption.
For example, if your application is backed by an advanced encryption standard (AES), whether it’s 128 or 256-bit, the ability to hack in would be far more difficult compared to an application with little or no encryption.
How Can Cybersecurity be Used to Protect Electronic Health Records (EHRs)?
At almost every intersection of healthcare and cybersecurity, providers will benefit from incorporating remote control security into their IT management plans. Many providers’ devices weren’t built with distanced care in mind, so the addition of secure remote access software will protect them as they take their work online.
Vulnerable EHR Systems
Countless devices collect, send, and store EHRs throughout healthcare institutions. And many of them were not designed with basic security features baked in. Here are just a few of the vulnerable EHR systems that could be compromised:
- Continuous glucose monitors (CGMs)
- Heart / vital sign monitors
- Ultrasound sensors
- Pulse oximeters
- Ventilators
- X-ray machines
- CT scanners
- Mammography units
- Digital diagnostic testing equipment
- Tablets, smartphones, smartwatches
The rapid convergence of healthcare and internet of things (IoT) has not kept up with adequate security. The IoT includes any physical device that is capable of connecting to other devices online: everything from tiny fitness wearables to towering linear accelerators.
Another CISA report from January 2020 revealed that several common GE medical devices were classified as “exploitable remotely/low skill level to exploit.” Even with industry-leaders like GE, providers have to take proper precautions with third-party manufacturers and the IoT devices they produce.
Importance of Secure Vendor Remote Access
Healthcare industry cybersecurity also depends on rigorous standards for vendor remote access. Healthcare vendors offer a multitude of different services which allow providers to focus more strictly on caring for patients. A few common examples of healthcare vendors are:
- Call centers for patient support and management
- Food service vendors for hospitals and medical office parks
- Marketing agencies
- Claims processing companies
- Custodial, laundry, and sanitation services
- Security systems
With more aspects of care, management, and general housekeeping being outsourced to third-party vendors, EHRs including personal health information (PHI) and personally identifiable information (PII) are no longer kept entirely in-house.


A recent Ponemon Institute study showed that 54% of healthcare vendors have experienced a data breach involving PHI. The average breach exposed around 10,000 records and cost $2.75 million. Vendor breaches often lead to costly changes, penalties, and legal fees for the healthcare organization, in addition to tarnished credibility. This is why it’s crucial for healthcare organizations to develop solid relationships with vendors, establish clear service level agreements (SLAs), and implement comprehensive remote access software.
9 Tips to Improve Cybersecurity with Your EHR Systems
Increasingly costly breaches in the medical sector demand a response from IT professionals and the public health entities they serve. A comprehensive plan is required to achieve optimal cybersecurity in healthcare. One effective solution is to add secure remote access software to your practice. Below, we’ve listed nine steps to improve cybersecurity in the healthcare industry, including secure remote access with your EHR systems:
1. Use Encrypted Channels for Patient Data
Only send patient data through secure, encrypted channels. This goes for remote monitoring of medical devices as well. An AES 256-bit encryption will ensure that even outside of your LAN, patient data stays protected.
2. Unique Firewalls for Unique Locations
For providers with multiple offices, it’s important that each location maintain its own unique firewall. Firewalls are designed to block unauthorized access while allowing outgoing communication.
3. Assess Risks and Patch Accordingly
Follow cisa.gov reports for the most up-to-date information of malware tactics, techniques, and procedures (TTP). This resource is critical for patching known vulnerabilities in your operating systems. In addition, understanding which devices are most likely to be outdated or high-risk is pivotal for determining which machines to use more strict remote access policies.
4. Implement In-depth Cybersecurity Training
For both healthcare workers and patients, training is key. Healthcare providers can require workers from doctors to custodians to complete cybersecurity training while instituting security awareness measures and campaigns for patients and their families.
5. Audit Your Acceptable Use Policy
Define acceptable use for each level of device, including mobile. A narrower scope for each level will help limit shadow IT.
6. Simulate Ransomware Attack Defense
From email filters and firewalls to MFAs and password strength, all lines of defense can be put to the test by running a tabletop simulation. These drills will help identify any weaknesses for common cyberattacks in healthcare.
7. Install and Test Strong Backup Systems
Ensure that data is backed up in more than one place–external and offline, as well as on the cloud. Maintaining backups will decrease leverage held by an attacker if a data breach occurs.
8. Adopt a Least-Privilege Approach to Administrative Access
Least-privilege is the practice of giving only the number of resources required to perform one’s job. Tighten access throughout your organization with levels of privilege and MFAs at each level. Your businesses’ remote access software should have strong authorization features and access controls that ensure only certain roles can access certain data and confirm that the person trying to gain access is who they say they are.
9. Prioritize Endpoint Protection on All Devices
Firewalls and encryption at every level of device will reduce risk and improve care. Choose a remote desktop software that can integrate with your technology stack and adapt to the needs of your practice.
Healthcare Cybersecurity and HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) predates the explosion of EHR systems seen in the last two decades. But HIPAA rules have been updated along the way to ensure individuals’ rights to privacy in healthcare.
In order to combat preventable HIPAA violations, providers and vendors alike need to optimize healthcare data security in two main venues: user access and user authentication.
Access to data for end users should be granted on a limited basis and followed up with strong authentication measures. Multi-factor authentication (MFA), password reset schedules, and lockouts should all be deployed to guarantee that the user is who they say they are.
Smaller healthcare organizations like clinics and testing centers may have limited IT resources making them a target for cyberattacks. To ensure proper cybersecurity in clinics, these organizations may want to consider a cloud-based security software that will protect them from costly HIPAA violations. While HIPAA is strictly US law, many countries have their own equivalent such as the General Data Protection Regulations (GDPR) in the EU.
On-Premise vs. Cloud-Based Access
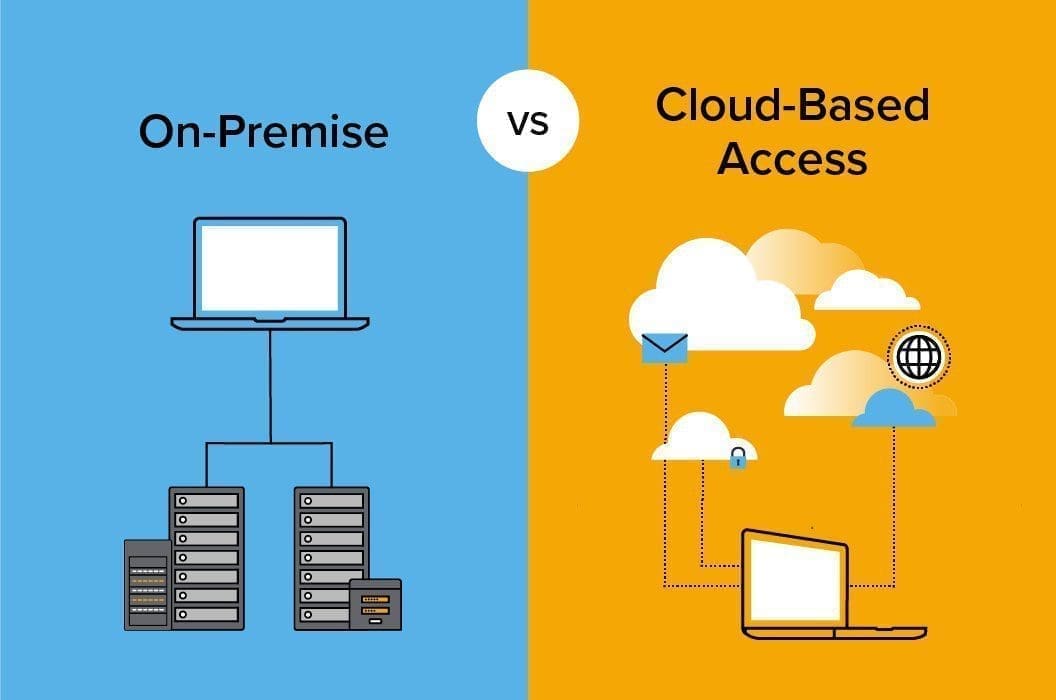
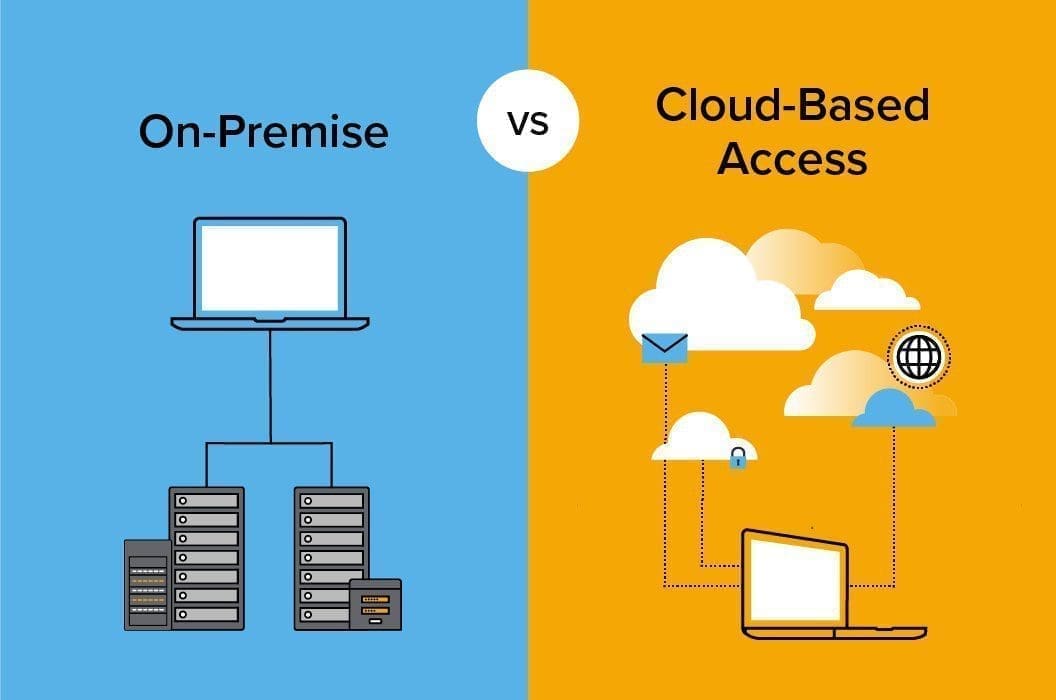
Cybersecurity in healthcare has followed the cloud-based trend while many still hold onto their on-premise models. So which option is right for your enterprise?
On-premise data systems favor complete control. Keeping everything on local servers means having an in-depth IT management plan. And while this may favor organizations with airtight cybersecurity protocols, it also requires in-house maintenance and monitoring from your IT team.
For many, cloud-based access will give organizations the security they need without having to assume the responsibility of a localized IT management plan. While cost is relative to each organization, many healthcare providers find that protecting their data with cloud-based access saves them time and money.
Use Impero for Healthcare Data Security
Across countless industries, Impero Connect has proven to be the most secure, scalable, and flexible remote access solution for businesses looking to improve their security online. Now, in a rapidly evolving industry, healthcare cybersecurity calls for secure access in order to avoid costly breaches and disruptions in care.
Some organizations already have access management plans in place but still have vulnerabilities in outdated OS, third-party services, and IoT devices. With Impero Connect, you can optimize your IT management plan by adopting a streamlined remote access solution that offers total security, efficiency, scalability, and compliance.
While other software solutions may be sufficient for a LAN, Impero Connect is designed to give your organization the flexibility it needs to operate over the internet anywhere, anytime. Whether you prefer cloud-based or on-premise data storage, you’ll be able to access EHRs from your devices remotely and securely. If you’re ready to find out more, contact Impero today and start your free trial!


