 Part 8 of 10 in our Complete Guide to Secure Remote Access in Retail.
Part 8 of 10 in our Complete Guide to Secure Remote Access in Retail.
Point of sale systems (POS) are at the heart of retail operations, from printing receipts to storing data, and everything in between.
For many retailers, managing common POS problems can be a challenge, including:
- Quickly troubleshooting
- Preventing and identifying data breaches
- Protecting personal information
- Remaining compliant with payment card standards
- Updating software
As the shift to cloud-based POS system continues, and retailers are expanding their operations nationally and globally, the need for remote access is crucial. Without it, organizations are unable to effectively grow, may experience increased downtimes that lead to lost sales, and put themselves at greater risk for security issues.
The advantages of remote access are numerous and we’re here to share five important reasons to make sure your organization chooses the most secure remote access solutions to protect and enhance your POS system.
1. Support for Legacy POS Systems
Many large organizations manage retail operations with older equipment and operating systems that may lack the necessary security to safely function in today’s fast-moving, regulated retail environment. While cloud-based POS systems have replaced many legacy POS systems, it is costly and time consuming to make the switch, leading some retailers to remain with their legacy systems.
Legacy POS systems manage data collection and storage on local servers through a closed, internal network. Because of this storage method, legacy systems can often be less secure and experience technical issues that may leave organizations scrambling to quickly troubleshoot and get back online. It’s difficult to keep legacy systems compliant with regulations like PCI DSS.
While cloud-based POS technology is useful, not all organizations are prepared to invest in an entirely new POS system–yet, they still need the POS benefits and security to keep business running.
That’s when secure POS remote access software is useful. By integrating with legacy POS systems that run software like Windows Mobile or Windows CE, remote access tools can offer organizations assurance that they are compliant, secure, and running at maximum efficiency.
2. Quickly Troubleshoot to Avoid Losing Sales
 Sending technicians onsite to troubleshoot problems is a considerable expense. An advantage of remote access is the immediate reduction in troubleshooting costs. A technician can login to a retailer’s network to:
Sending technicians onsite to troubleshoot problems is a considerable expense. An advantage of remote access is the immediate reduction in troubleshooting costs. A technician can login to a retailer’s network to:
- Identify problems
- Take control of screen
- Resolve issues
- Make updates to operating systems and applications
- Detect changes that may indicate data leakage or security gaps
This is particularly important because retailers need their POS systems to conduct transactions. Any delay in service is money lost–and the longer that delay continues, the more costly it becomes. If a technician needs to travel to a location to troubleshoot, retailers not only lose time, but incur travel expenses. They can also use remote access to fix a machine remotely or push patches ff-hours when the machines are unattended.
Remote access for POS systems ensures that transactions can continue without interruption, software updates are made regularly, and that any security gaps are identified and/or addressed before they cause problems that could interrupt daily operations.
3. Single Solution for Variety of End-User Machines
Within retail environments, especially large organizations, there are a vast array of end-user machines and technologies being used. And not just by the retailer, but by their vendors who need specific access to their network.
This can present a challenge: how do retailers keep all these different aspects of their network secure and running efficiently?
By integrating with legacy POS systems that run older versions of Windows or Linux, remote access tools can offer organizations fast, flexible, secure access. It also means that users can easily connect to any devices from a single user support interface.
Additional benefits of remote access solutions that are consolidated into one tool are:
- Customized security credentials
- Multi-factor authentication
- Granular user access for vendors
- Decrease overall costs of maintaining multiple solutions
4. Manage Security of Personal Identifiable Data (PID)
While primary account numbers (PANs) are still most valuable to attackers, they are increasingly interested in gathering PID from POS machines. With personal data, attackers can exploit information or sell it for profit.
Information like PANs are PCI-regulated, so cloud POS systems typically provide excellent security already–but PID information is often less secure because it is not PCI-regulated. That means that PID is more vulnerable to attack and needs additional security.
One of the benefits of remote access is that it minimizes security vulnerabilities related to PID in addition to existing security found in cloud POS systems. More specifically, secure remote access tools can offer the following encryption measures that enhance security:
- Encryption and decryption keys needed to access data
- Encrypted connections
- Encrypted data from end-to-end
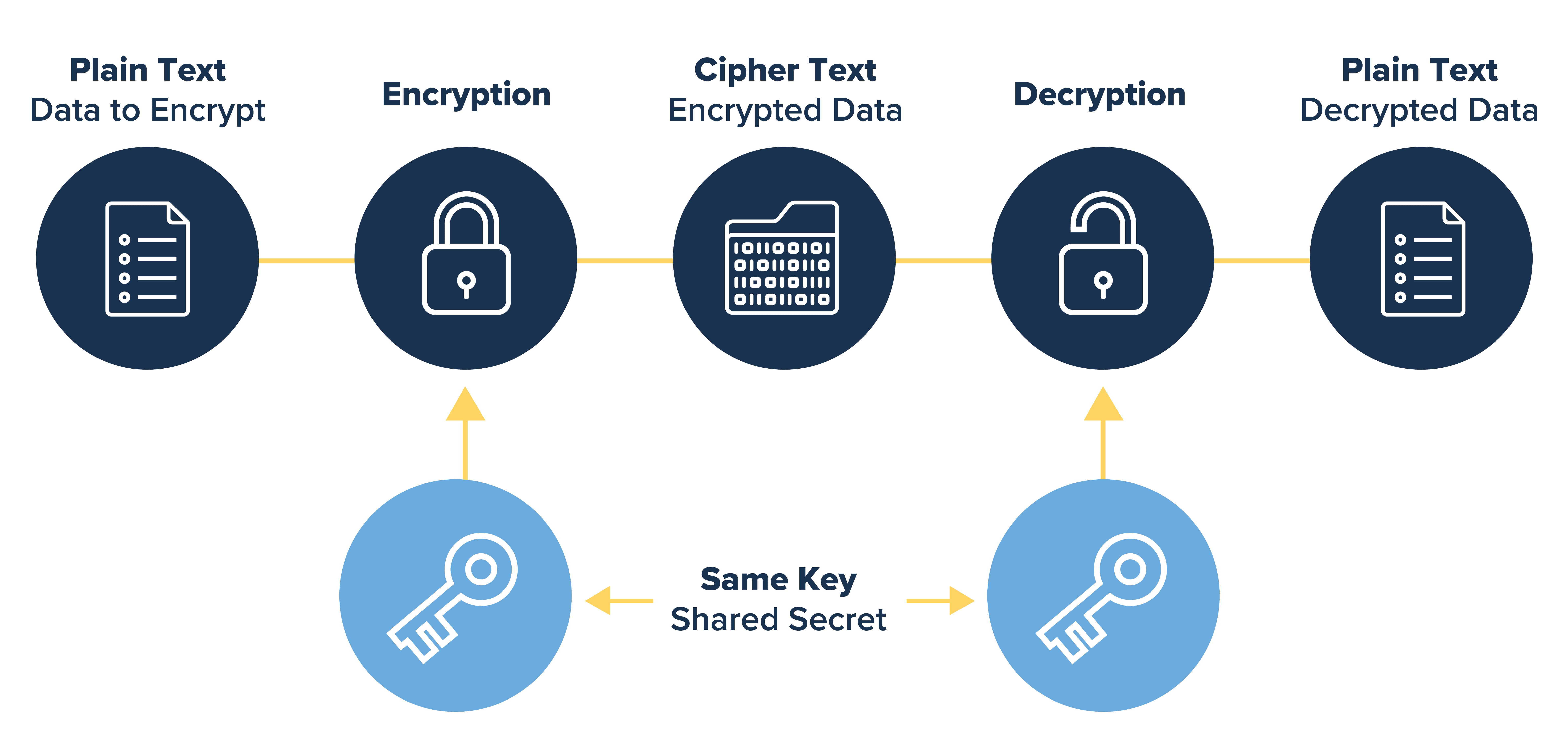 The highest levels of encryption include those that use 256-bit AES, which is particularly effective at preventing brute force (trial and error) attacks. The 256-bits means that there are 2256 possible combinations, which would take an immense amount of time to crack, even with the most advanced technology. With secure remote access, retailers can feel confident that both PAN and PID are safe from attackers.
The highest levels of encryption include those that use 256-bit AES, which is particularly effective at preventing brute force (trial and error) attacks. The 256-bits means that there are 2256 possible combinations, which would take an immense amount of time to crack, even with the most advanced technology. With secure remote access, retailers can feel confident that both PAN and PID are safe from attackers.
5. Extensive Logging for Efficiency and Compliance
One of the many advantages of remote access is the ability to log everything, whether it be for analysis or auditing purposes. This gives context to what’s occurring on a network at any given time and also allows for thorough reporting.
In particular, video logging can be incredibly useful for retailers to identify patterns, problems, data breaches, and opportunities for training. If remote access solely relies on text-based logs, there may be gaps in information, especially if there is screen sharing involved.
Retailers are under strict regulations because they process credit card and personal data. Regulations like those included in PCI DSS have logging requirements that are critical in preventing, detecting, and minimizing access to data.
Relying on a fully compliant remote access solution can help retailers avoid violations and ensure compliance throughout their POS system. Compliance is a constant effort, and particularly important as organizations grow and expand into new geographical regions.
While remote access software does not guarantee compliance everywhere, it’s a valuable tool to make the logging process more efficient and give administrators the information they need to protect retail POS environments.
Benefits of Remote Access in One Solution
Finding one remote access solution that offers all the benefits above is pivotal for efficient business operations they can be found in Impero Connect.
The advantages of remote access that Impero provides, include industry-leading platform support for a variety of operating systems and advanced security features that help manage vendor access, an important aspect of retail operations.
Learn more and get a free trial of Impero Connect and see all the benefits that a secure remote access solution can provide.



