Take these steps to secure your remote access and avoid being the next victim.
North Country Business Products, a Point of Sale (PoS) services and solutions company based in Minnesota, announced a data breach on February 20, 2019.
Full details have not been released, but it has been reported that attackers breached North Country’s IT systems and were able to install malware on over 135 locations – including restaurant, bar and coffee shop PoS systems throughout the Midwest. So far, there have been no public reports of stolen data being misused, but officials are concerned because the malware was able to harvest cardholder names, credit card numbers, expiration dates and CVV information.
Unfortunately, attacks like this on PoS systems are nothing new. According to the Trustwave Global Security Report for 2018, PoS systems within the retail and hospitality industries were the target of choice for hackers around the world last year. Increasingly, these attacks are coming from service providers and vendors like North Country Business Products. Hackers have figured out that attacking one MSP can deliver data from dozens or even hundreds of different businesses.
The retail and hospitality industries have been hit hard by data breaches over the past few months. In November 2018 we learned that more than 500 million individuals had personal data stolen during the breach of Marriott-owned Starwood Hotels. In December 2018, Caribou Coffee announced a breach affecting over 200 of their locations.
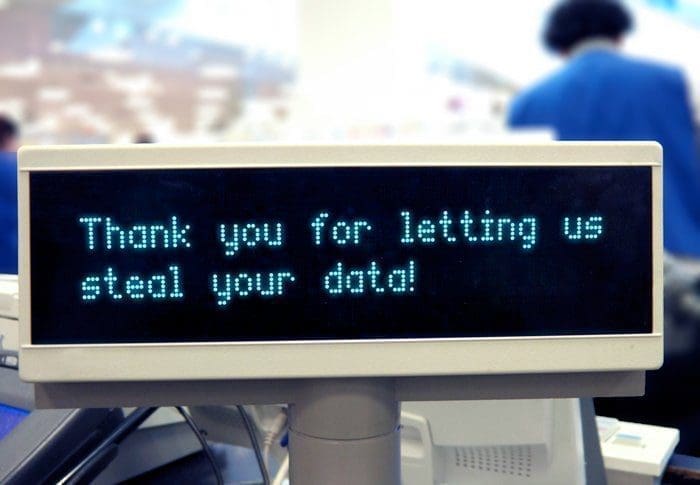
It’s not hyperbole or fear-mongering when we say “hackers are coming for your data.” It’s clear. They are. Knowing that hackers look at remote access as a weakness to exploit, be careful about which tools you’re using.
Secure Your Remote Access Software
Forensic analysis of the data breaches at Marriott, Caribou Coffee and North Country Business Products have not been made public, so we can’t know exactly what went wrong. But it’s clear remote access software is a frequent vector in these attacks.
It’s not always simple to address the risks, but at the very least you should be looking at secure alternatives to remote access tools with well-known issues. Popular tools like Microsoft’s Remote Desktop Connection Manger, TeamViewer and VNC have well-known security vulnerabilities that have led to high-profile data breaches. Hackers target these solutions for infiltration into networks and/or exfiltration of data once a breach has occurred.
Download our free workbook – Securing Remote Access: Basic & Advanced Strategies
Virtual private networks (VPN) are ubiquitous in today’s IT landscape, but they include risks that are often overlooked or accepted by IT departments. If your business relies on a vendor like North Country Business Products to service and support your organization, using remote access software is a requirement. Fortunately, you can take steps to secure your remote access software and prevent PoS attacks.
Best practices to protect your PoS systems
No one can promise you total protection against hackers. As quickly as the security professionals devise new strategies and defenses, the hackers devise new ways to attack our systems. That said, there are things you can do to minimize the risk of an attack on your business.
1. Talk to your service providers. Attacks on service providers are on the rise. We all rely on vendors to help manage our equipment, our systems and our network connectivity. If you haven’t started a conversation with your vendors about data security, do it immediately. What tools are they using to access your network? What controls do they have in place? How are they monitoring their infrastructure and their users to ensure compliance with established policies and procedures? We place a lot of trust in these providers, so make sure you verify they are using best practices to support your business.
2. Layer your defenses. There is no single activity or strategy for developing good data security. You need multiple lines of defense. Some of those defenses should include….
3. Segment your network into defined security zones. Isolate and defend network segments where sensitive data is secured. For example, PoS devices shouldn’t be accessible by the “average” user. I’ve seen instances where a POS system was using the same WiFi as store employees – even guest users – which is a recipe for disaster. Make sure devices with sensitive information are closed off from other users and other devices. Wall them off on completely different network segments using VLANs, firewalls and subnets.
4. Choose the appropriate tools. This step is a tough one. What does “appropriate” even mean? Choosing the right tool for the job requires consideration, research, and more discussion with your service providers. Do you really need to provide VPN access to the entire network, or would secure remote control to a single device be better? Using freeware, or a low-cost tool bundled with another piece of software might sound good, but does it open you to additional risk? Remember, if your vendors are using those tools they are putting you at risk.
5. Implement strong access controls for your staff and especially for third parties, vendors or service providers who access your network. Developing strong access controls is a well-documented subject. Take the time to research controls most appropriate for your organization. Those controls will likely include:
- Require devices to authenticate to the network using security tokens or secure deployment options
Sett a maximum number of invalid password attempts for users - Enforce time-outs that disconnect inactive users
- Restrict access by IP and/or MAC address
- For attended devices, make sure the local user must confirm remote access before it is granted
- Whitelist applications for users
- Establish date and time controls
6. Enforce multi-factor authentication before access is granted to devices or network locations where sensitive data is stored.
7. Use granular permissions to ensure authenticated users have the right permissions on the right devices.
8. Ensure data is encrypted when it is stored and that all your access tools use point-to-point encryption for data in transit.
9. Log all activity. Most systems include the ability to log events, actions, and processes running on a device. Make sure your log files also include user sessions. Again, this is especially true for service providers, vendors or any user accessing a device remotely.
If you are interested in learning more about protecting your PoS systems, visit our website or reach out and schedule a conversation with one of our experts. Security is the cornerstone of our remote access software and Impero has over 30 years of experience working with retailers.
Impero Connect is used by nearly a quarter of the largest retailers in the world, 50% of the Fortune 100 and 60% of the largest companies in Europe. We can help you too.


